Technical overview
How REDDCRYPT works
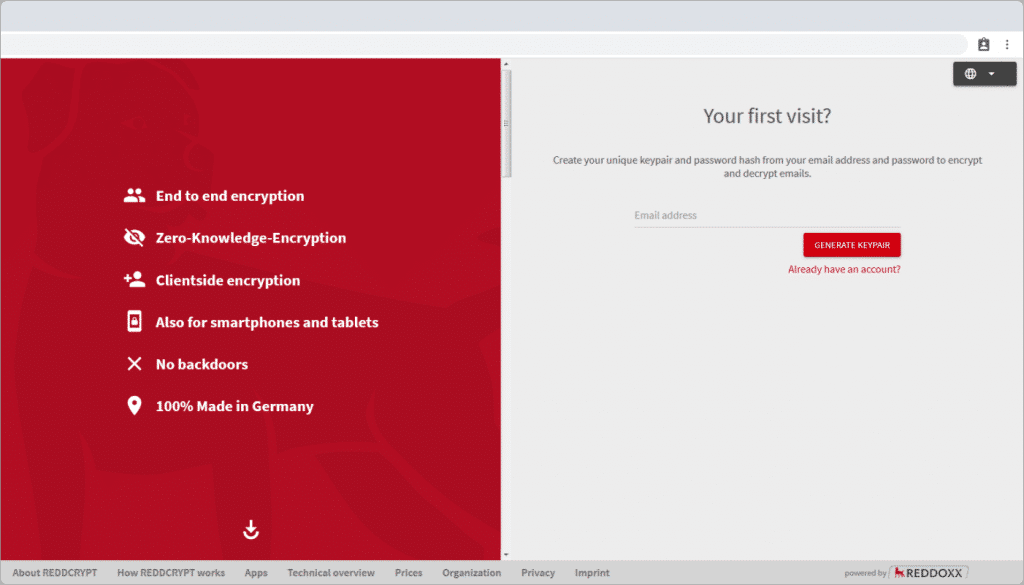
REDDCRYPT is based on the PGP encryption method. This means that our solution works with a respective certificate pair – consisting of a private and a public key. However we solve the biggest problem that the established standards have: they are not operable for a “normal” (non-technical) user!
The difference between REDDCRYPT and other solutions: The entire handling of the certificates takes place automatically in the background. No user ever has to deposit a certificate somewhere or even know how the technology works. And with this approach we make e-mail encryption usable for everyone!
On this page we explain to you in detail and completely transparently how the encryption and decryption of REDDCRYPT works.
Quick overview: This happens at REDDCRYPT
REDDCRYPT automatically encrypts your emails on your device before they are being sent. Thus, your emails and their contents remain private. This way you can securely send sensitive information via email.
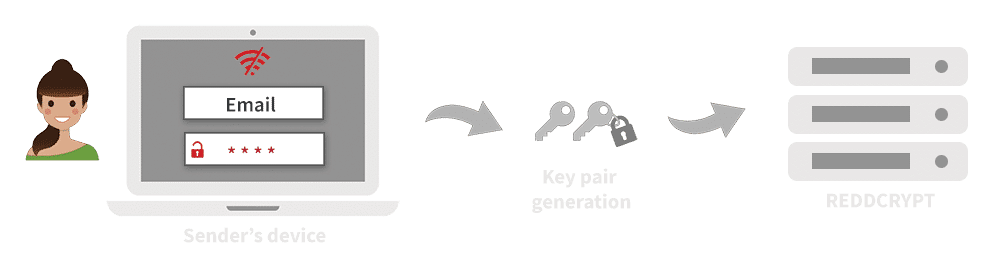
You authenticate yourself on the REDDRYPT app with your email address and a password. A key pair comprising of public key and private key is automatically generated. Your private key is then encrypted with a password hash and uploaded to our servers together with your public key.
Sounds too complicated? Don’t worry as most of this happens in the background. You only need to enter your email address and choose a password to generate the key pair.
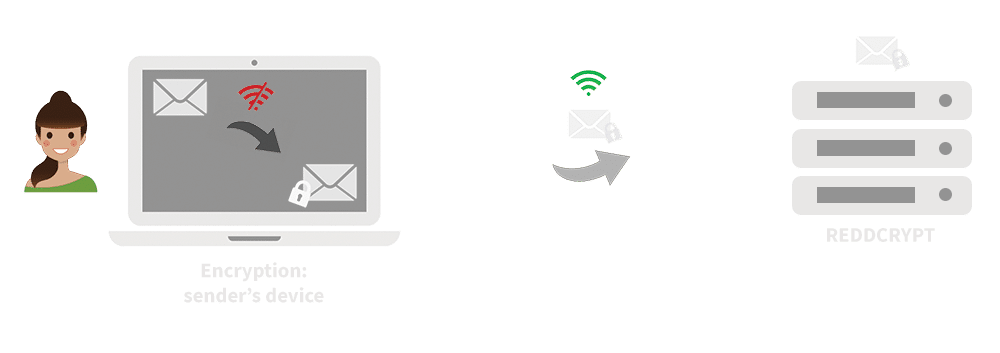
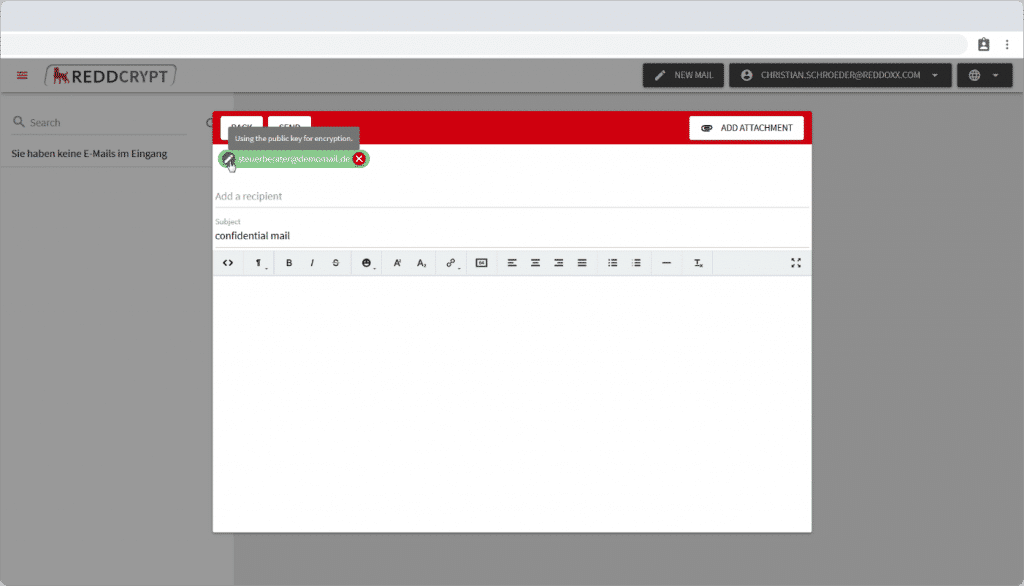
Writing an email happens locally on your device. Why is this important you may ask? Because only you can read the contents of the email as the process happens locally. Before sending the email it is automatically encrypted on your device.
If the recipient is also a REDDCRYPT user, the encryption takes place with the public key of the recipient. This means that you don’t have to take action, as everything happens automatically in the background.
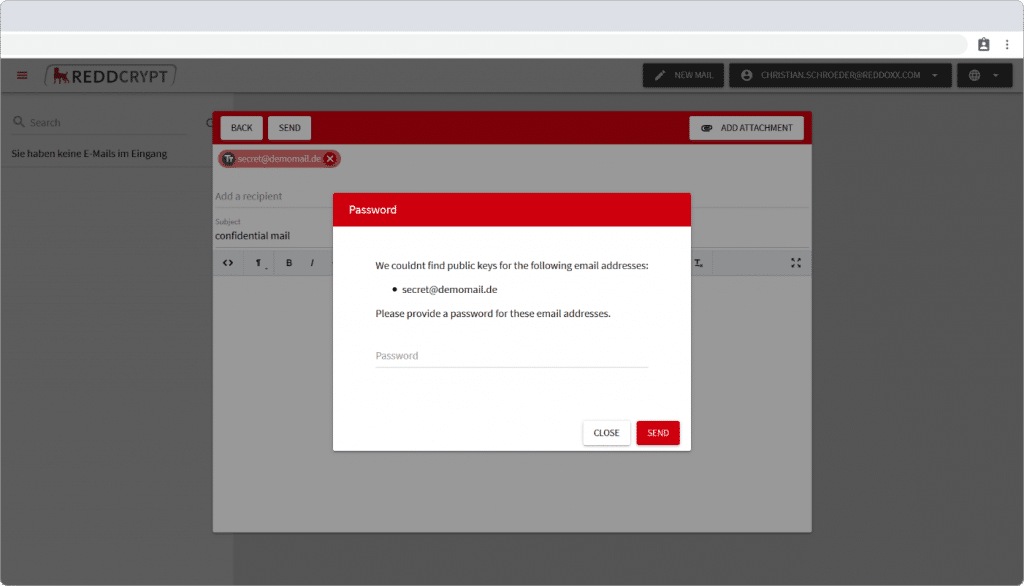
If the recipient is not a user of REDDCRYPT yet, you will have to define a passphrase for this first mail with which the recipient can decrypt the mail. To make sure that only the intended recipient can read your email. you can disclose this passphrase to the recipient e.g. via sms or phone call.


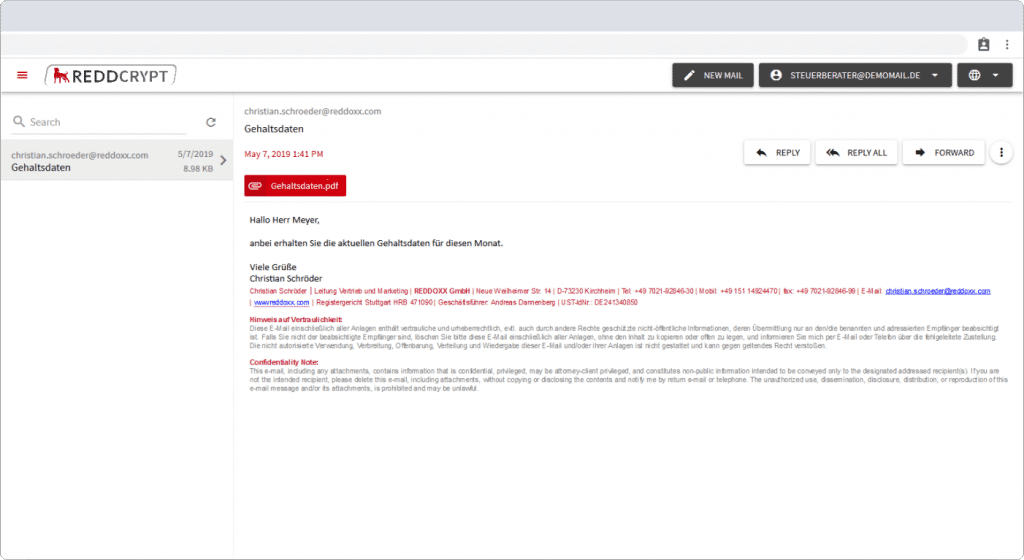
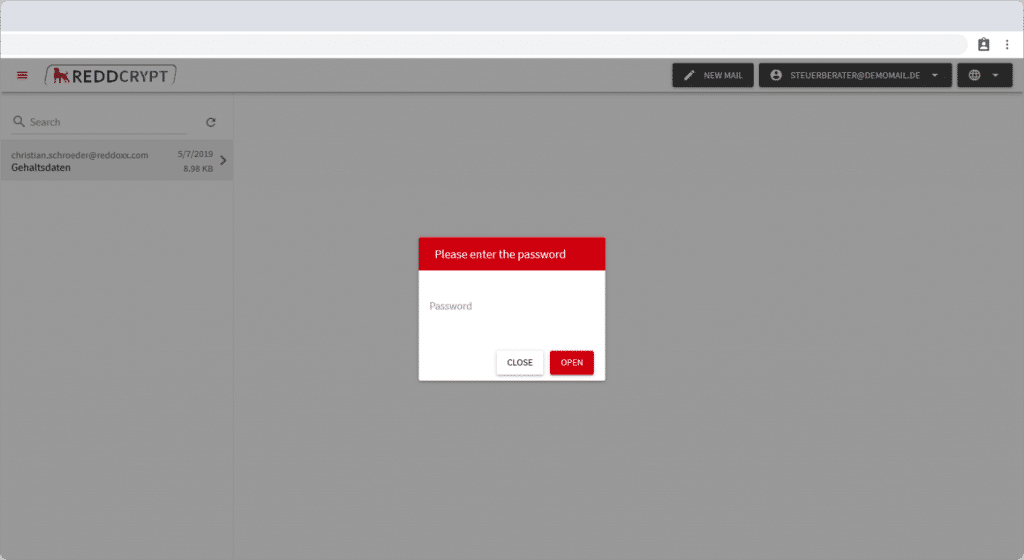
To be able to read the email the recipient authenticates on the REDDCRYPT app, as well. If he already has access and the email has been encrypted with this public key, then the recipient can open, read and answer your mail right away. If he didn’t have access yet, he will have to generate his own key pair to through his email address and a chosen password. Afterwards he can see your encrypted email which can be encrypted by entering the passphrase you have disclosed to the recipient earlier (e.g. via sms or phone call).
This passphrase is only necessary for the decryption of the first email. With every email that comes afterwards the encryption and decryption process takes places automatically in the background. Highest user comfort and highest security – this is REDDCRYPT.
In detail
Creating a key pair at the beginning
Every REDDCRYPT user generates a key pair when first using REDDCRYPT. This RSA key pair consists of a private and a public key and is generated from the combination of the user’s email address and a chosen password.
The generation of the key pair takes place locally on your device.
After confirming that the User is the owner of the email address, he/she assigns his/her personal password. This password is used to encrypt the users private key and at the same time a password hash is generated from this password via a key derivation.
The password hash is necessary to authenticate the user in the REDDCRYPT app. We use a hash value so that the actual password of the user is never transferred and not stored in our database. Furthermore, a hash value is much more secure as it has higher entropy – more randomness – compared to passwords in plain text.
The encrypted private key is transferred to REDDCRYPT together with the public key.
Data protection: What data we store and how we protect it
Fundamentally, the REDDOXX App serves to store and transfer encrypted emails. For our service to work smoothly and on different devices we have to store some data.
Email Address
The email address is required to log in to the REDDCRYPT app.
Public Key
We store your public key unencrypted. This is uncritical as public keys don’t contain any sensitive information. It is in their nature to be unencrypted so that other users can use them to send you encrypted emails.
Private Key
Your private key has already been encrypted locally on your device with your password. This encrypted private key is transferred to us and stored securely.
Password Hash
In order to encrypt and decrypt an email the REDDCRYPT user’s password is mandatory. This password has already been hashed on your device and is hashed again on our servers.
Encrypted Email
To improve the user experience we store encrypted mails on our servers. This allows recipients to access and read emails instantly from any device via web browser. Emails have already been encrypted in a container on your device before being transferred to us.
What if REDDCRYPT were hacked?
Zero knowledge – Full control over your emails
REDDCRYPT is a so-called zero-knowledge provider. All private and sensitive information are fully encrypted before being transferred to REDDCRYPT. The important thing about about the zero-knowledge technique is the fact that we neither know your password nor is it being transferred to us at any point. Thus, we do not have access to your emails.
The encryption and decryption of your emails happens 100% locally on your device.
Every decryption starts with the user’s password which is necessary to decrypt the private key, which – again – is necessary to decrypt the encrypted email.
This is further evidence of the zero-knowledge technique as your keys, despite being stored on our servers, can only be used in combination with your password.
Only your public key is stored unencrypted on our servers so that other REDDCRYPT users can use it to send you encrypted emails.
Security – Your password stays with you
As mentioned, the encryption and decryption of the emails only works if you authenticate with your email address and password in the REDDCRYPT App. Your password never leaves your device. As part of the zero-knowledge technique
Your password is needed in two cases: To authenticate in the REDDCRYPT app and to decrypt your private key. As part of the zero-knowledge technique a password hash is generated from your password through key derivation.
When logging in to the REDDCRYPT app a password hash is derived from the combination of your email address and a password and then transferred to us. If the hash value matches the hash value stored on our servers, access to your encrypted emails will be granted. If the hash value does not match access will be denied.
In order for the emails to be automatically decrypted on your device the password is used.
The authentication process for accessing the REDDCRYPT app
If a user accesses the REDDCRYPT app, the following happens:
- A password hash is derived from the password entered on the user’s device
- The entered email address and password hash are sent to the REDDCRYPT server
- The password hash is hashed again on the server
- On the server the hashed password hash is compared to the hash value stored in our database. If both values match, the entered password is correct and the user’s authentication is successful.
If the user’s authentication is successful he is granted access to the encrypted emails. To decrypt these emails the private key is needed which is automatically downloaded in the background to your device and decrypted with the password.
Why happens when clicking the 'Forgot Password' option?
Functionality: Client-side encryption
After successful authentication a random session key is generated on the user’s device with which the email is encrypted for the first time. To make sure that nobody else besides the recipient gains access to the email’s content, the session key is also encrypted.
Recipient is already REDDCRYPT user
Upon entering the recipient’s email address a request is send to REDDCRYPT’s key server. If the recipient is already a user of REDDCRYPT, his public key is already stored on our servers and is downloaded to encrypt the session key.
Recipient is not yet a REDDCRYPT user
If no public key is available for the entered email address the sender has to define a random passphrase with which the session key is encrypted.
On Sending
When the REDDCRYPT user clicks send the encrypted email and the encrypted session key are bundled in a container which is then transferred to the REDDCRYPT server.
Functionality: Client-side decryption
How the email is decrypted depends on whether the recipient has already been a REDDCRYPT user at the time of the email’s sending.
The recipient is already a REDDCRYPT user and has a key pair
After the recipient’s successful authentication on the REDDCRYPT app the private key and container are downloaded. Afterwards, the private key is decrypted with the password. The password is now used to to decrypt the session key.
The decrypted session key is used to decrypt the encrypted email. The complete process takes place in the background and the email opens automatically afterwards.
The recipient is not a REDDCRYPT user yet and does not have a key pair
The user generates a key pair for authentication on the REDDCRYPT app. This process is similar to a traditional registration process for the user. Afterwards the user authenticates on the REDDCRYPT app and the container is downloaded in the background.
As the session key has not been encrypted with a public key but with a passphrase this passphrase is needed for decryption. After the passphrase is correctly entered the decrypted session key is used to decrypt the email.
REDDCRYPT Business and the Master-Key
Administrators of REDDCRYPT Business can create a master key for their organisation and thus protect their own company against data loss.
Because this master key enables the decryption of all emails of the own company, a requirement that occurs again and again, especially after employees have left the company. The master key also enables employees to create a new password if they forget their old one.
This is changed by the Master-Key
If an organisation has a master key users’ private keys are no longer encrypted directly with the users password.
From the user’s entered password – from which the password hash was derived at the beginning – a further hash value is now determined: a password key. In the future the users private key will be encrypted with this password key instead of the password.
The creation of the Master-Key
If a Master-Key is created basically the same happens as when creating a REDDCRYPT account: If the administrator creates a master key it is created locally on the administrators device.
In addition the administrator defines a password from which a password key is derived here as well. With this password key the master key is encrypted and transferred to our servers in encrypted format.
Again without the password defined by the administrator the master key cannot be used. This is an essential part of the Zero-Knowledge technology and does not differ from the process described above which is applied to the user keys. Since the defined password is never transmitted to us only you can use the master key.
This is how the Master-Key works…
If an organisation has a master key the users password key is additionally encrypted with this master key. So in the future there will be two ways to decrypt the users private key: By the users password input and by the master key.
…if emails should be decrypted
For example if e-mails from employees who have left the company need to be decrypted this can be done using the master key.
- To do this the master key has to be decrypted using the password created by the administrators
- Afterwards the decrypted master key is used to decrypt the users password key
- The decrypted password key is used to decrypt the users private key
- The decrypted private key is used to decrypt the email.
We have described how the complete process looks like in practice in our Knowledge Base: https://www.reddcrypt.com/en/knowledge-base/decrypt-emails-of-former-employees-with-the-master-key/
… if passwords are forgotten
If a user has forgotten their password they can generate a new password without losing access to previously encrypted emails. During the development phase it was important for us that the administrators do not know the user passwords so we developed a process that allows the user to define his new password on his own.
To do this the user creates a new password using the “Forgot Password” function which is first stored temporarily in encrypted form. To use the new password the users private key must be decrypted and then re-encrypted with the new password.
- The administrator enters the password of the master key to decrypt it
- With the decrypted Master-Key the (old) password key of the user is decrypted
- The decrypted password key is used to decrypt the users private key
- A new password key is generated from the users new password
- The users private key is encrypted with the new password key
- The password key is encrypted with the master key
- The process is finished and the new password can be used for login from now on
How the whole process looks like in practice we have described in our Knowledge Base: https://www.reddcrypt.com/en/knowledge-base/resetting-password-with-master-key/

